Mac Mini to the Cloud: Building Your Own Private Cloud Workstation
- Published on
- ...
- Authors

- Name
- Huashan
- @herohuashan

Foreword
As a programmer, I've been thinking about how to flexibly manage my personal development environment while protecting company data security. The company's HBI computers have strict information security monitoring, which is of course necessary, but it also means my personal projects, learning materials, and development tools are not suitable for the company computer.
After some experimentation, I found a perfect solution: place a Mac Mini at home, use intranet penetration technology to make it "go to the cloud", enabling access anytime, anywhere. This article will detail my entire setup process.
Part 1: Why Choose This Solution?
1.1 Transition from Cloud Desktop to Self-hosted Solution
Initially, I tried using cloud desktop services, configured with Ubuntu 8GB+128GB, annual fee 500+ yuan. But after using it for a while, I found several issues:
- Continuously rising costs: First-year newcomer price was acceptable, renewal price significantly increased
- Insufficient performance: Often froze after installing VS Code, Chrome, Zotero, Obsidian and other tools
- Frequent restarts needed: When connection failed, needed SSH login to restart services
1.2 Advantages of Mac Mini Solution
Eventually, I chose to purchase a Mac Mini M4 (24GB + 512GB) as a private cloud host:
✅ Cost Advantages
- One-time purchase, no annual fee
- Extremely low electricity cost (M-series chips have very low power consumption)
- Small configuration Alibaba Cloud ECS as jump server (mainly for traffic forwarding)
✅ Performance Advantages
- M4 chip has strong performance, completely sufficient
- 24GB memory, no pressure for multitasking
- Local storage, fast read/write speed
✅ User Experience
- At home: LAN direct connection, almost no latency
- Away: Relay through Alibaba Cloud Shanghai ECS, also low latency (same city)
- Complete data control: All data in your own hands, safe and controllable
✅ Additional Features
- Can serve as soft router: Manage home network through Surge
- 24/7 online services: Can run automated scripts and services
Part 2: Solution Architecture Design
2.1 Overall Architecture Diagram
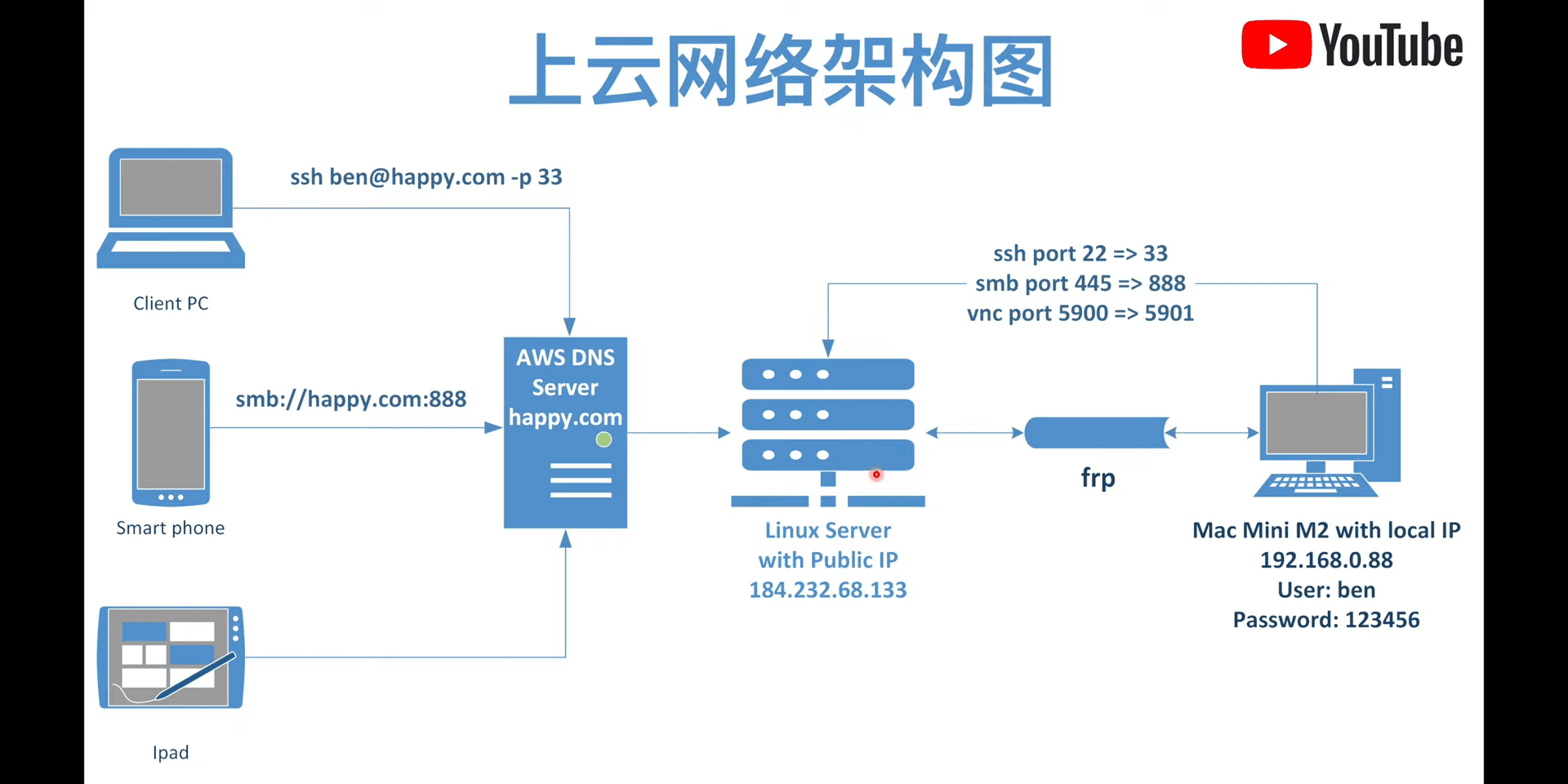
2.2 Core Component Description
Hardware Devices:
- Mac Mini M4: Placed at home, as the actual work host (internal network device)
- Alibaba Cloud ECS (Shanghai): As public network jump server, enables intranet penetration
Why Choose Alibaba Cloud Shanghai ECS?
Geographic location is key! I live in Shanghai, choosing a same-city server has huge advantages:
- Extremely low latency: Usually within 10ms
- Good stability: Same ISP network, less packet loss
- Reasonable cost: Small configuration sufficient (1 core 2GB enough), mainly for traffic forwarding
Software Service Architecture:
| Service | Purpose | Deployment Location |
|---|---|---|
| FRP | Intranet penetration (core) | ECS server + Mac Mini client |
| RustDesk | Remote desktop control | ECS server + Mac Mini client |
| Tailscale DERP | Virtual LAN relay | ECS server |
| Surge | Soft router management | Mac Mini |
2.3 Working Principle
┌─────────────┐ ┌──────────────────┐ ┌─────────────┐
│ External Access │ ────▶ │ Alibaba Cloud ECS │ ◀──── │ Mac Mini │
│ (Office/Cafe)│ │ (Public jump server) │ │ (Home internal network) │
└─────────────┘ └──────────────────┘ └─────────────┘
Public IP: xxx.xxx.xxx.xxx Internal IP: 192.168.x.x
Core Principle:
- Mac Mini actively connects to Alibaba Cloud ECS, establishing persistent tunnel
- ECS listens on specific ports, waiting for external access requests
- External requests are forwarded to Mac Mini through ECS
- Achieves "intranet penetration", Mac Mini gains public network access capability
Part 3: Hands-on Practice: Setup Steps
3.1 Alibaba Cloud ECS Server Configuration
Alibaba Cloud ECS is the key node of the entire solution, serving as a public jump server allowing the internal Mac Mini to be accessed from external network.
Step 1: Deploy FRP Server (Core)
FRP is the core tool for achieving intranet penetration. First confirm server architecture:
lscpu | grep "Vendor ID"
wget https://github.com/fatedier/frp/releases/download/v0.62.1/frp_0.62.1_linux_amd64.tar.gz
tar -zxvf frp_0.62.1_linux_amd64.tar.gz
cd frp_0.62.1_linux_amd64
sudo cp frps /usr/local/bin/
sudo mkdir /etc/frp
sudo cp frps.toml /etc/frp/
Configure FRP Server (/etc/frp/frps.toml):
[common]
bind_port = 7000 # FRP service port
vhost_http_port = 8081 # HTTP virtual host port
vhost_https_port = 443 # HTTPS virtual host port
dashboard_port = 81 # Management panel port
[auth]
method = "token"
token = "your_secure_token" # Please change to your secure token
[dashboard]
auth_method = "password"
user = "admin"
password = "your_password" # Please change to your password
[webServer]
addr = "0.0.0.0"
port = 81
Configure System Service (/etc/systemd/system/frps.service):
[Unit]
Description=Frp Server Service
After=network.target
[Service]
Type=simple
User=root
Restart=on-failure
RestartSec=5s
ExecStart=/usr/local/bin/frps -c /etc/frp/frps.toml
[Install]
WantedBy=multi-user.target
Start FRP Service:
sudo chmod 644 /etc/systemd/system/frps.service
sudo systemctl daemon-reload
sudo systemctl enable frps # Enable auto-start
sudo systemctl start frps # Start service
sudo systemctl status frps # Check status
Step 2: Deploy RustDesk Service
RustDesk provides remote desktop functionality. Deploy using Docker:
Install Docker:
apt update
apt install -y docker.io docker-compose-plugin
systemctl enable --now docker
Create RustDesk Configuration:
mkdir -p /opt/rustdesk && cd /opt/rustdesk
# Create docker-compose configuration
cat > compose.yml << 'EOF'
services:
hbbs:
container_name: hbbs
image: rustdesk/rustdesk-server:latest
command: hbbs -r YOUR_SERVER_IP:21117 # Replace with your ECS public IP
environment:
- ALWAYS_USE_RELAY=Y
volumes:
- ./data:/root
network_mode: "host"
depends_on:
- hbbr
restart: unless-stopped
hbbr:
container_name: hbbr
image: rustdesk/rustdesk-server:latest
command: hbbr
volumes:
- ./data:/root
network_mode: "host"
restart: unless-stopped
EOF
# Start service
docker compose up -d
# Get public key (needed for client configuration)
docker logs hbbs | grep Key
# Or
cat /opt/rustdesk/data/id_ed25519.pub
Step 3: Deploy Tailscale DERP Relay
DERP provides relay service for Tailscale, optimizing network connection:
docker pull ghcr.io/yangchuansheng/ip_derper:latest
docker run --restart always \
--name derper \
-d \
-p 59443:443 \
-p 3478:3478/udp \
ghcr.io/yangchuansheng/ip_derper:latest
Step 4: Configure Security Group (Firewall)
Open the following ports in Alibaba Cloud console security group:
| Service | Ports | Protocol | Description |
|---|---|---|---|
| FRP | 7000, 81, 8081, 443 | TCP | FRP service and management panel |
| RustDesk | 21115-21119 | TCP | RustDesk signaling server |
| RustDesk | 21116 | UDP | RustDesk data transmission |
| DERP | 59443 | TCP | Tailscale DERP HTTPS |
| DERP | 3478 | UDP | Tailscale DERP STUN |
3.2 Mac Mini Client Configuration
Step 1: Configure FRP Client
Download FRP Client:
Download corresponding version based on Mac processor type:
- M-series chips: frp_0.61.1_darwin_arm64.tar.gz
- Intel chips: frp_0.61.1_darwin_amd64.tar.gz
Configure Client (frpc.toml):
[common]
server_addr = "YOUR_ECS_IP" # Replace with your ECS public IP
server_port = 7000
[m4_auth]
method = "token"
token = "your_secure_token" # Keep consistent with server configuration
[m4_transport]
protocol = "tcp"
tls_enable = true
# SSH port mapping
[ssh]
name = "ssh"
type = "tcp"
local_ip = "127.0.0.1"
local_port = 22
remote_port = 222 # Access Mac Mini SSH via ECS_IP:222
# NoMachine remote desktop port mapping
[nomachine]
name = "nomachine"
type = "tcp"
local_ip = "127.0.0.1"
local_port = 4000
remote_port = 4001 # Access NoMachine via ECS_IP:4001
First Run:
cd ~/Downloads/frp_0.61.1_darwin_arm64 # Enter extracted directory
sudo ./frpc -c ./frpc.toml
Note: First run may prompt "unable to verify developer", need to go to
System Settings → Privacy & Securityto manually allow running.
Configure Auto-start:
Create LaunchAgent configuration file:
# Create configuration directory
mkdir -p ~/Library/LaunchAgents
# Create configuration file
cat > ~/Library/LaunchAgents/com.frp.frpc.plist << 'EOF'
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<key>Label</key>
<string>com.frp.frpc</string>
<key>ProgramArguments</key>
<array>
<string>/Users/huashan/Documents/Frp/frpc</string>
<string>-c</string>
<string>/Users/huashan/Documents/Frp/frpc.toml</string>
</array>
<key>RunAtLoad</key>
<true/>
<key>KeepAlive</key>
<true/>
<key>StandardErrorPath</key>
<string>/tmp/frpc.err</string>
<key>StandardOutPath</key>
<string>/tmp/frpc.out</string>
</dict>
</plist>
EOF
# Set permissions and start
chmod 644 ~/Library/LaunchAgents/com.frp.frpc.plist
launchctl load ~/Library/LaunchAgents/com.frp.frpc.plist
launchctl start com.frp.frpc
Tip: Remember to change path
/Users/huashan/Documents/Frp/to your actual location for storing frpc.
Management Commands:
# Stop service
launchctl stop com.frp.frpc
# Restart service (after modifying configuration)
launchctl stop com.frp.frpc && launchctl start com.frp.frpc
# Remove auto-start
launchctl unload ~/Library/LaunchAgents/com.frp.frpc.plist
rm ~/Library/LaunchAgents/com.frp.frpc.plist
Step 2: Configure RustDesk Client
Configure in RustDesk client:
- Open RustDesk settings
- Click "Network" tab
- Fill in following information:
- ID Server:
YOUR_ECS_IP:21115 - Relay Server:
YOUR_ECS_IP:21117 - Key: Public key content obtained from ECS server
- ID Server:
Step 3: Mac Mini System Settings
To ensure stable remote access, need to adjust some system settings:
Prevent Sleep:
System Settings → Lock Screen → Turn display off...→NeverSystem Settings → Energy→ Enable all
Enable Remote Services:
System Settings → General → Sharing- ✅ Screen Sharing
- ✅ File Sharing
- ✅ Remote Login
- ✅ Remote Management
- ✅ Content Caching
Auto-login (Optional):
System Settings → Users & Groups→ Enable auto-login
Part 4: Daily Use and Maintenance
4.1 Server Management
View Service Status:
# View all Docker container status
docker ps
# View FRP service status
systemctl status frps
# View RustDesk logs
docker logs hbbs
docker logs hbbr
# View DERP logs
docker logs derper
Restart Services:
# Restart FRP
systemctl restart frps
# Restart RustDesk
cd /opt/rustdesk && docker compose restart
# Restart DERP
docker restart derper
Backup Configuration:
# Backup RustDesk data (contains public key and other important info)
tar -czf rustdesk-backup-$(date +%Y%m%d).tar.gz /opt/rustdesk/data/
# Backup FRP configuration
tar -czf frp-backup-$(date +%Y%m%d).tar.gz /etc/frp/
4.2 Troubleshooting
Issue 1: FRP Connection Failed
# Check service status
systemctl status frps
# View logs
journalctl -u frps -f
# Check if port is occupied
netstat -tlnp | grep 7000
# Check firewall
iptables -L -n | grep 7000
Issue 2: RustDesk Cannot Connect
# Check container status
docker ps
# View detailed logs
docker compose logs -f
# Re-obtain public key
cat /opt/rustdesk/data/id_ed25519.pub
# Check port
telnet YOUR_ECS_IP 21115
Issue 3: Mac Mini Client Disconnect
# View FRP client logs
cat /tmp/frpc.err
cat /tmp/frpc.out
# Restart client
launchctl stop com.frp.frpc && launchctl start com.frp.frpc
4.3 Performance Optimization Recommendations
Network Optimization
- Use BBR acceleration:
echo "net.core.default_qdisc=fq" >> /etc/sysctl.conf - Adjust connection limit: Adjust ulimit according to actual use
- Use BBR acceleration:
Security Hardening
- Change default ports
- Use strong passwords and complex tokens
- Regular system and service updates
- Configure fail2ban to prevent brute force attacks
Monitor Alerts
- Use Uptime Kuma to monitor service availability
- Configure DingTalk/Enterprise WeChat alerts
Part 5: User Experience and Summary
5.1 Actual Use Scenarios
Scenario 1: Working at Office
- Remotely connect to home Mac Mini via RustDesk
- Latency about 20-30ms (Shanghai same city)
- Can smoothly use VS Code, Terminal and other development tools
Scenario 2: At Cafe
- Connect via SSH (FRP penetration)
- Use tmux to maintain sessions
- Experience close to local development
Scenario 3: Business Trip Away
- Establish secure connection via Tailscale
- DERP relay ensures connection stability
- Access home materials anytime
5.2 Solution Advantages Summary
✅ Low Cost
- Mac Mini one-time investment about ¥5000+
- Alibaba Cloud ECS lightweight configuration monthly fee about ¥50
- Annual total cost much lower than cloud desktop subscription
✅ Strong Performance
- M4 chip performance far exceeds same-price cloud hosts
- Local storage, no worry about cloud storage speed limits
- 24GB memory, no pressure for multitasking
✅ Extremely Low Latency
- Same-city server, ping value within 10ms
- LAN direct connection at home, almost no latency
- Remote desktop experience close to local operation
✅ Data Security
- Data completely controlled in your own hands
- No worry about cloud service provider privacy issues
- Complete separation of work and personal data
✅ Strong Scalability
- Can add hard drives for expansion
- Can run various automated services
- Can serve as soft router to manage home network
5.3 Some Thoughts
This solution is not perfect, also has some limitations:
⚠️ Issues to Note:
- Home network stability affects user experience
- Cannot access during power outage or network failure
- Need some Linux operation and maintenance knowledge
- Initial configuration needs some time
🔮 Future Improvement Directions:
- Configure UPS uninterruptible power supply
- Add automatic fault recovery mechanism
- Optimize network performance and security
- Explore more automation scenarios
5.4 Final Words
From cloud desktop to self-hosted private cloud, this solution perfectly solves my needs:
- Complete separation of work and personal data
- Access own development environment anytime, anywhere
- Cost-controlled, excellent performance
- Data security, complete control
If you also have similar needs, might as well try this solution. Although initial configuration needs some time, in the long run it's definitely worth the value.
Hope this article helps you! If you have any questions, welcome to discuss in comments.
Related Resources:
- FRP Official Documentation: https://github.com/fatedier/frp
- RustDesk Official Documentation: https://rustdesk.com/docs/
- Tailscale Documentation: https://tailscale.com/kb/
Series Article Preview:
- Next article will introduce how to configure complete development environment on Mac Mini
- Will share some automated scripts and efficiency tool usage tips later
Update Log:
- 2025-11-14: Completed first draft
- To be updated: Add video demonstration
Photo by Samuel Angor on Unsplash